Let’s dive into the vast world of MFA, and all the different methods of identity verification that you might encounter.
Author: Alex

Every time you change devices, you could be putting your data at risk.

Having a robust data backup and recovery system is the best way to ensure you can recover all your most important data, in the event of a cyberattack or hardware failure.

Tech giants like Meta and Google are questioning the future of AI — and so are lawmakers around the world.

Understanding and addressing privilege escalation risks is essential to preventing breaches.
What is privilege escalation and how can you protect yourself against this vulnerability?

While you may have learned how to spot and avoid ransomware attacks, or what to do when your data is illegally encrypted, how much do you know about WHY you shouldn’t pay ransom fees?
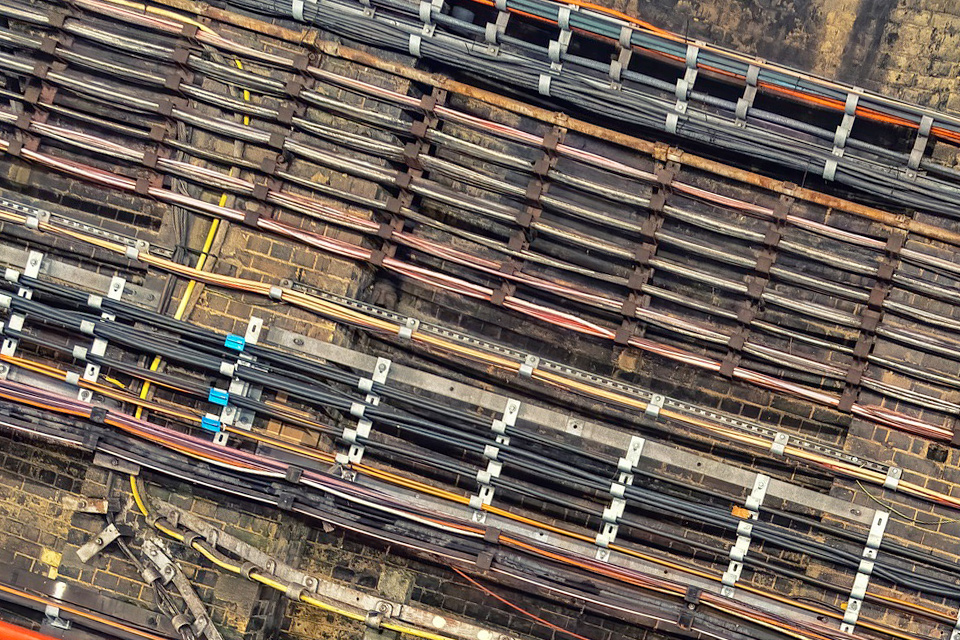
In the Baltic Sea, undersea cables essential for global internet connectivity were sabotaged! Why do bad actors attack undersea cables?

Today, we’re diving into some emerging and persisting insider threats to be on the lookout for in 2025!

How do cyberattacks affect the day-to-day worklife for individuals who work there, and what happens when clients and customers are affected? What long-term effects can we see?

Even if you’re not in a tech role, understanding what a firewall does and why it’s important can help you make smarter choices to stay secure online, both at work and at home!

