SaaS companies commonly face risks having to do with service interruption or data breach events. Learn how to manage them inside.
Category: Cybersecurity

Many implement the latest antivirus software, data encryption protocols, and firewalls. But what happens if malware is introduced into the system from inside? i.e. by an employee.

Ransomware is all over the news. In here, we’ll review the details of these attacks and what your business can do to protect itself.
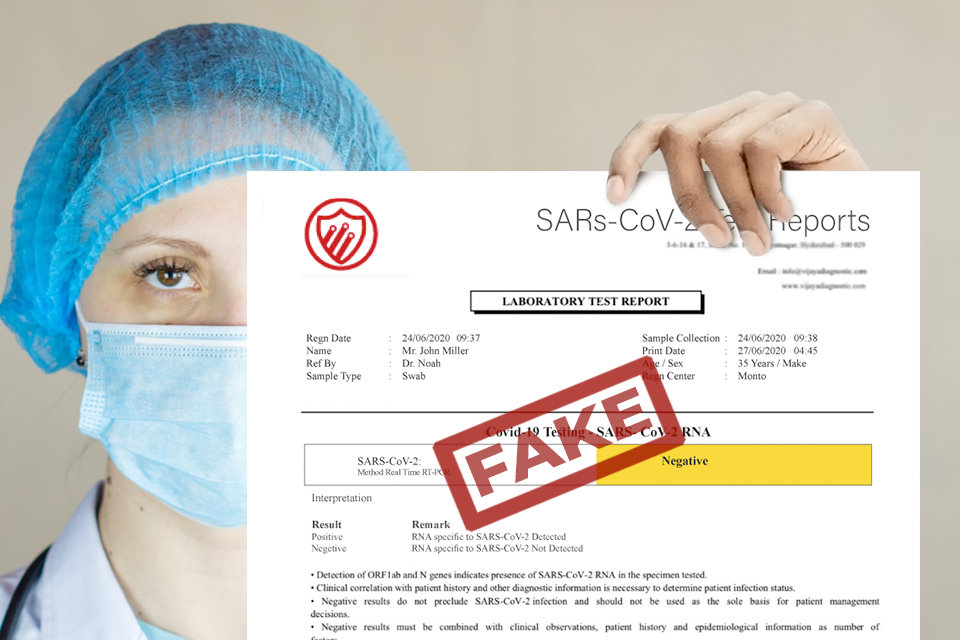
As vaccination becomes more commonplace, bad actors are developing false proofs of vaccination to sell on the black market.
A new botnet called EwDoor has been recently discovered targeting AT&T devices based in the U.S.

A data breach could bottleneck your progress indefinitely or cause you to shutter. Here’s how to protect your growing company.

The tech sector will have to reckon with entirely new travel expectations, not just for right now, but for the foreseeable future too.

Monitoring and protecting your work accounts may not be enough to prevent a cyberattack. The tidbits gathered from your personal pages can be just as damaging.

As more cybersecurity jobs become available, ask yourself: Are we hiring the skills we actually need?

Phishing: It’s the last thing anyone wants to fall for and one of the most prevalent threats to businesses today.

