Introduce
Have you ever been browsing online, when your web browser sudden throws up a red screen emblazoned with a warning that the site you’re trying to access has detected vulnerabilities which could leave you exposed to malware?
Depending on what browser you prefer, the page may look something like this:
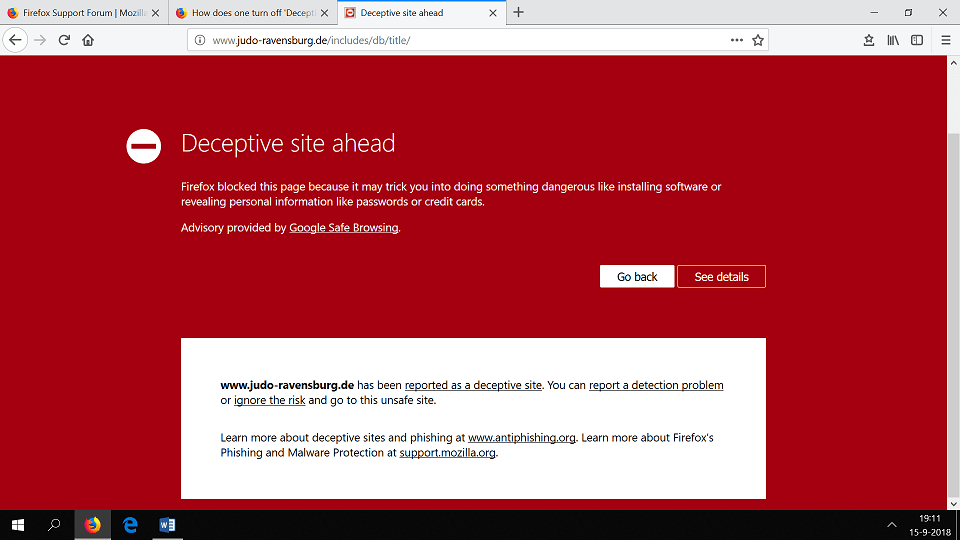
If you’ve ever been tempted to ignore the risk and go ahead to the deceptive site, then this blog post is for you.
Different Types of Web Filtering
Throughout your life, you may have encountered web filtering in various forms. They might look like blocked websites or locked photographs. Some you can easily bypass at your own risk; others, like parental controls, are determined by the network administrator above your head. This is more generally known as content control software.
Think about some of the sites accessible to you on your office’s WiFi. Can you log into Facebook? Reddit? All these may be blocked via web filtering software that monitors the network and every device connected to it, overriding your personal accessibility controls. This may be done to keep you on task and protect your confidential data from exposure.
Why Use Web Filtering
Although it can be frustrating to have your own browsing obstructed, these filters provide a more secure online experience compared to relying on your own instincts to tell malicious sites from benign ones. Web filtering automatically protects…
- Corporate policies
- Data security
- Compliance with federal regulations
- Content and DNS filtering
- Anti-phishing efforts and other social engineering techniques
All of this is meant to take the burden of threat detection off of yourself, so you can focus on work instead.
When to Turn Off Web Filters
Sometimes you need to adjust your security settings. If you leave your job, for example, there’s no need to keep their network permissions on your devices. Alternatively, you can allow certain programs or websites through the filter so there is no trouble going there in the future, if you know for sure that they are safe.
You can also handle it on a case by case basis. Remember the red screen from earlier? Depending on your permissions, you may be able to manually “ignore the risk” and proceed to the landing page you were looking for. However, you need to be very careful about when to choose this option. Firstly, understand why the message pops up: In most cases, it’s because the website does not use the secure HTTPS:// prefix or your browser has detected high risk levels on that page, or even received reports of phishing attempts originating from there.
So when should you proceed? Once you read to understand the risks, check that you have correctly entered the URL and that the domain name matches. Cybercriminals often alter a letter or two in the hopes you won’t notice the typo. Make similarly few exceptions to the type of site that you give carte blanche to load, as they could become compromised at any time and open you up to an infection or breach.
Conclusion
Web filtering is there for a reason: Supplementing your cyber-protection. As the Internet and the behavior of its users change over time, web filters must evolve to keep up with new threats, trends and security measures. For this reason, the industry is expected to continue growing over at least the next five years, as more people seek digital protections online.
What programs do you rely on for web security? The answer may differ for work versus personal use, or even by machine. IoT devices are typically less cyber-secure than your home computer, so they are a common target for hackers. You might download antivirus apps that monitor the web to warn of potentially unsafe sites; there is more than one approach to web security and filtering. You can never be overly cautious when it comes to Internet threats.
Hopefully now you have a better understanding of why web filtering matters and how it protects you from suspicious or high-risk content online. The more you understand about the risks present on the Internet, the better prepared you can be to spot, recognize and avoid threats. Web filtering is another important tool in your belt.
Follow our blog for the answers to all of your most pressing cybersecurity questions!
References